Ivanti Unified Endpoint Manager is an application that helps its users to manage all their profiles with the help of its all-in-one management software. This application eases its users with the surety of managing their files on their device without any data loss and provides its users complete security of their confidential business files with its day zero support.
It handles all the profiles of its users on all the devices including Linux to Chrome OS, windows to macOS, and also beyond loT, all thanks to its developers and a talented tech team who created this endpoint manager for us. Like other alternatives, it also provides guidelines on how to use it efficiently in the form of a demo and apply it in a free trial to get experience before use.
Features
- Client-based UEM
- Manage modern and traditional devices
- Contact team service
- Help remote workers
- Increase IT productivity
- Automate provisioning
Similar to Ivanti Unified Endpoint Manager
There are up to 21 Ivanti Unified Endpoint Manager Alternatives. It has features like Linux. The best alternative to 21-ivanti-unified-endpoint-manager-alternatives is SiSoftware, which is Free. The other best apps like 21-ivanti-unified-endpoint-manager-alternatives are Oomnitza, Incident IQ and Spiceworks.
Pricing
Ivanti Unified Endpoint Manager Information
21 Best Ivanti Unified Endpoint Manager Alternatives
Filter Alternatives
1Oomnitza
Oomnitza is a solution for Enterprise Technology Management that gives users access to a critical business process system for endpoints, apps, infrastructure, and networking. It ensures that your technology is optimal, secure, and compliant from when you buy it to when you retire it. In many ways, this will change the way our company moves forward. Every person we've worked with has been very professional and has helped us a lot in our efforts to get the most out of…
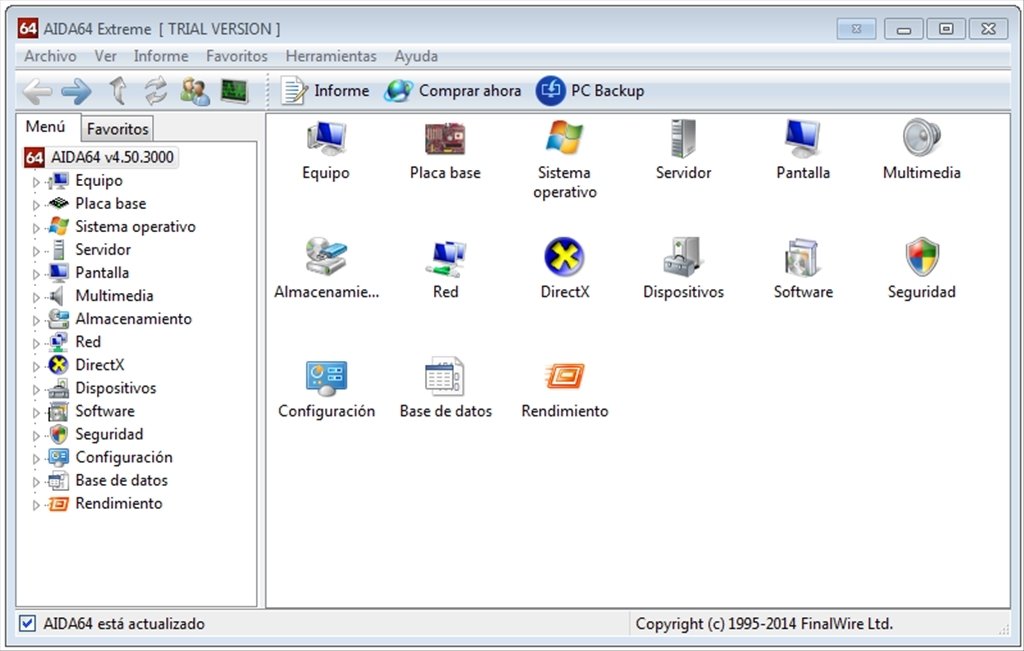
2AIDA64
The company FinalWire Ltd. developed AIDA64, which is a diagnostic and auditing tool. It gives information about Windows, Android, iOS, Windows Phone, Tizen, Chrome OS, and Sailfish OS, as well as these operating systems themselves. All AIDA64 benchmarks have been updated to 64-bit and now use MMX, 3DNow, and SSE instructions. It makes it possible to test Intel and AMD multi-core processors in more depth. So that the benchmarks are as accurate as possible, this was done. There have been…
Advertisement
3Spiceworks
Spiceworks is a professional network for people who work in IT. Its headquarters are in Austin, which is in the state of Texas. It is an online community where people can work together and help each other. It also gives its users access to a market where they can buy and sell IT-related goods and services. It is thought that about six million people who work in information technology and three thousand different types of businesses in the technology industry…
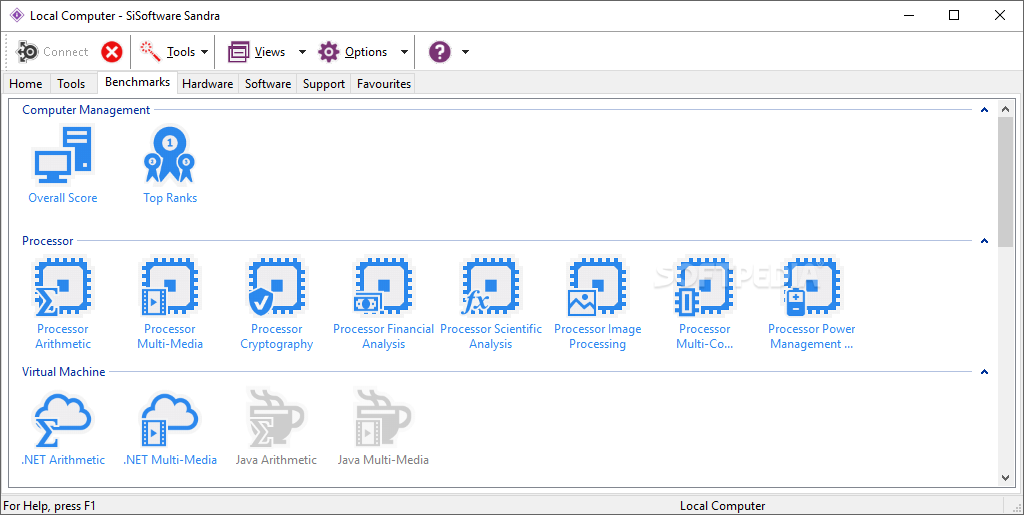
4SiSoftware
SiSoftware Developed by SANDRA, a piece of software that can be used for analysis, diagnosis, and benchmarking. It's benchmarks show off new technologies like multi-core, WMMX2, WMMX, AMD64/EM64T/x86-64, IA-64, NUMA, SMT, SMP, SSE4, SSSE3, SSE3, SSE2, SSE, MMX, Java, and.NET. It is a tool for Windows that helps you analyze and fix problems on your PC. Your PC's model and the technical specs of its different parts, such as its CPU, graphics card, storage, network adapter, and Internet connection, are…
Advertisement
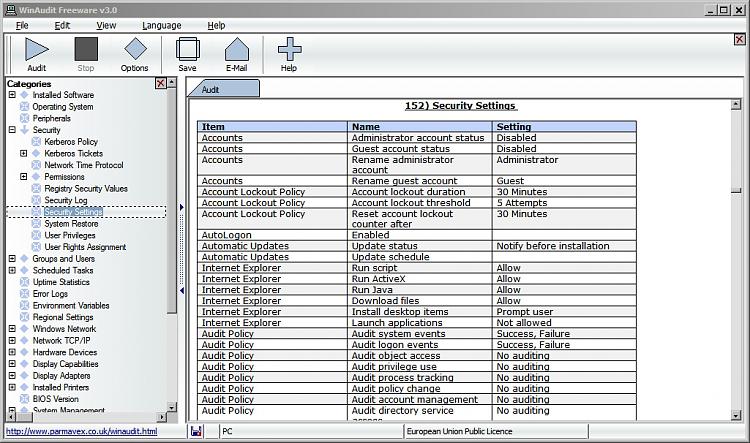
5Winaudit
Using WinAudit, you can check your computer's hardware, software, security settings, networks, and more. It makes a detailed report about the system's settings, hardware, and software. The software may report on the system's hardware and software configuration. The results are shown on web pages divided into sections for easy reading and text-based searching. It has features for people interested in software auditing, tracking hardware, technical support, security, or even being curious. The program can keep an eye on Windows updates…
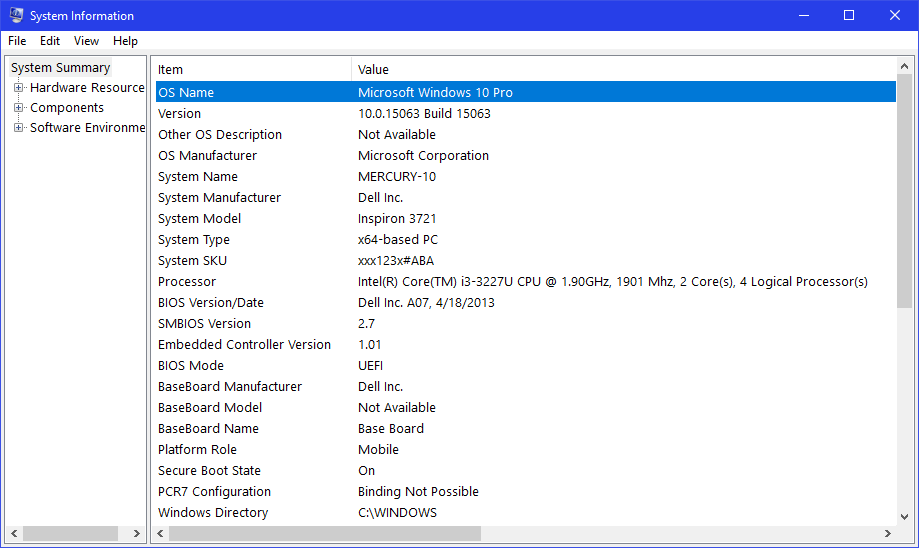
System Information is a system profiler that comes with Microsoft Windows. It shows information about the operating system, hardware, and software that can diagnose and fix problems. The Control Panel is where you can find System Information. All Windows computers come with it already set up. It gathers technical information about the whole system, the hardware resources (like RAM and I/O), the actual hardware parts (like CD-ROM, sound, and network), and the Windows environment as well (drivers, environment variables, services,…
Advertisement
IT service management (ITSM), IT asset management (ITAM), and other digital operations in K–12 schools are all transformed by Incident IQ. IT support staff can do their jobs faster and better with the help of Incident IQ. Streamline how devices are given out, take care of school-related costs, and more. Through Incident IQ's connection to Google Devices, IT departments at K-12 schools can automatically assign devices, see a lot of metadata, and lock Chromebooks that have gone missing without touching…
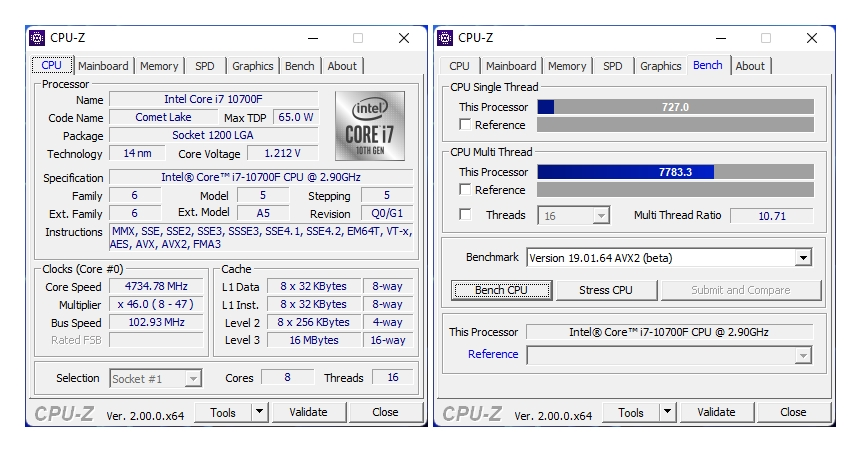
8CPU-Z
CPU-Z is a free Microsoft Windows and Android tool that lets you profile and watch your system. It can figure out a modern PC or Android device's central processing unit, random access memory, motherboard chipset, and other hardware parts. CPU-Z is better in almost every way than the tools that come with the Windows operating system for identifying hardware parts. So, it helps identify some features without having to open the case. In particular, it helps determine the core revision…
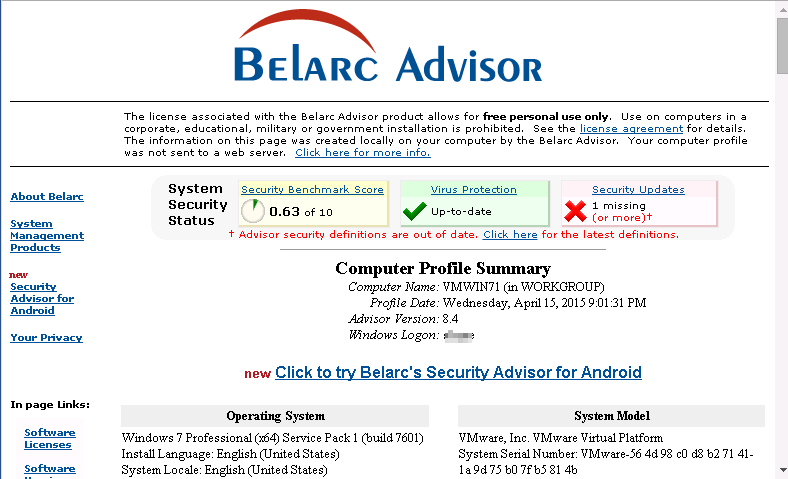
9Belarc Advisor
The Belarc Advisor uses your computer's Internet connection to make a complete profile of your system's software, hardware, network, missing Microsoft hotfixes, antivirus status, and security benchmarks. Information you put in your profile on your computer is never sent to a server elsewhere. It is faster, more accurate, and gives more detailed information than similar programs, some of which even charge for the same features. Belarc Advisor is an excellent choice if you need a tool to quickly and thoroughly…
Panda AD360 is an endpoint protection platform that offers comprehensive security features, including endpoint detection and response (EDR) and patch management. It helps users block malicious apps, manage security patches, filter web content, and more. Panda Adaptive Defense 360 evaluates the attributes of executables to classify them as safe or harmful.
Cisco provides secure client-based remote access, allowing employees to connect to their company's network securely from any location, without compromising security. The platform offers flexible, policy-driven access via wired, VPN, and wireless connections, ensuring visibility and control over the devices used to access the network.
12Harmony Endpoint
Harmony Endpoint is an endpoint security solution designed to protect remote workers from complex threats. It blocks harmful threats like phishing, ransomware, and drive-by malware, providing quick autonomous detection and response. Harmony Endpoint offers robust protection, helping organizations maintain high security standards efficiently.
Microsoft Defender (also known as Microsoft Defender Advanced Threat Protection) delivers enterprise-level security to prevent, detect, investigate, and respond to advanced threats. The platform includes post-breach detection, preventative protection, and automated investigation capabilities, helping organizations quickly respond to security incidents.
Singularity is a platform that enables users to create and run containers, which encapsulate software in a portable, networked environment. It allows users to build containers on their systems and deploy them across various HPC clusters globally, including local university clusters, company servers, cloud environments, and workstations.
15Trend Micro XDR
Trend Micro XDR is a cybersecurity tool that offers extended detection and response (XDR) capabilities. Integrated with Trend Micro Vision One, it provides threat intelligence, data collection, and correlation. Trend Micro XDR also offers threat detection, event response, forensic investigation, and detailed reporting, helping businesses protect against security breaches.
Advanced Endpoint Protection helps protect systems from complex threats like file-less and zero-day attacks using behavioral analysis and machine learning. It offers a variety of endpoint security tools, including firewalls and antivirus software, to detect attacks based on threat intelligence, providing early warnings about potential threats.
17SentinelOne
SentinelOne is a cybersecurity program that helps organizations detect, block, and respond to threats using artificial intelligence. It provides visibility into network traffic and applies self-defense mechanisms to protect data integrity. SentinelOne also enables businesses to secure their workflows by defending against various attack vectors.
Endpoint Protector is a data protection solution focused on preventing data loss across multiple operating systems. It provides monitoring, data discovery, and protection services, controlling portable devices like USB drives based on device identifiers, ensuring that sensitive data is kept secure.
19CrowdStrike Falcon
CrowdStrike Falcon is an endpoint security platform powered by machine learning and artificial intelligence. It offers protection against malware-free and file-less attacks, securing data and network infrastructures. The platform integrates threat intelligence, allowing organizations to monitor their security posture proactively and respond to threats before they breach systems.
ManageEngine Desktop Central is a Windows desktop management tool that allows users to manage servers, smartphones, desktops, and other devices from a central location. The platform offers services such as software deployment, patch management, remote desktop sharing, and Active Directory management, simplifying IT administration for businesses.
21Cybereason
Cybereason is an endpoint protection platform designed to detect and respond to security breaches. It combines next-generation antivirus, endpoint detection and response (EDR), and managed monitoring services. Cybereason uses in-memory graphs and automated hunting engines to efficiently detect malicious activities and behavioral patterns across endpoints. Founded by elite intelligence professionals, Cybereason is an online endpoint protection platform that offers users endpoint detection and response against security breaches. Users can also get help from next-generation antivirus, managed monitoring services, and more.…