Google Duo is a beautiful, agile, and responsive video calling software with excellent voice quality. People all over the world may use this software to talk and express their emotions with just one click. Google Duo is a simple and dependable application that works on both iOS and Android smartphones, and it’s also likely to work on the web.
Long-distance communication has never been easier, but Google Duo makes calling and seeing your loved ones a breeze. This lavish program also allows you to participate in conference calls; all you have to do is click on the URL provided.
Features
- Share Videos
- Voice messages
- Video Calling
- End-to-End Encryption
- Video Conferencing
Similar to Duo
There are up to 7 Duo Alternatives for several platforms, including Playstore, Apple. The best alternative to 7-duo-alternatives is Google Authenticator, which is Paid. The other best apps like 7-duo-alternatives are Yubico, Azure Multi-Factor Authentication and Authy.
Pricing
Duo Information
7 Best Duo Alternatives
Filter Alternatives
1Yubico
Yubico Authenticator enables users to securely store TOTP and HOTP credentials on a YubiKey, offering portable, multi-platform authentication. Developed by Yubico Inc., this program supports OATH credentials for major platforms like Google Apps, Amazon, Hotmail, Dropbox, Microsoft, and more. Even if your phone is compromised, your credentials remain safe when stored on a YubiKey.
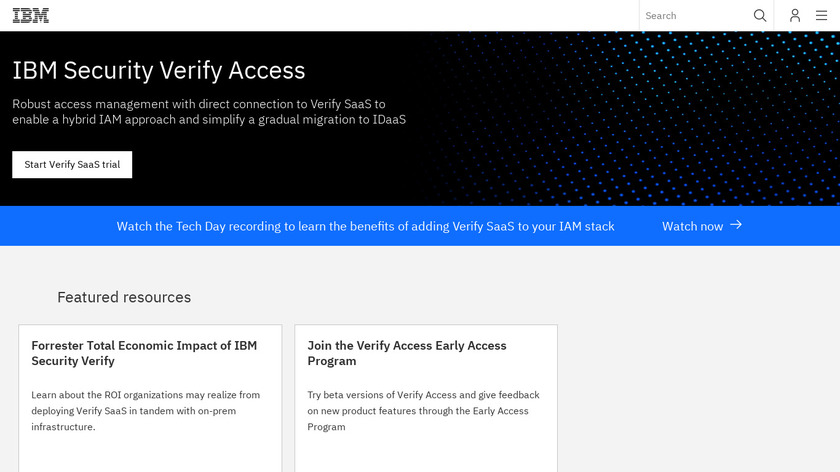
IBM Access Manager is an all-in-one identity and access management platform that includes a suite of technologies for securely extending data centers to the Internet. Customers may use this solution to govern access and usage rights across a variety of resources, such as file servers, websites, databases, e-mail, Web Services, application hosting, apps, Web content, mobile devices, virtual machines, and more. Its robust network security safeguards networks, individual PCs, services, and businesses. With multi-cloud compatibility, it comes with the necessary…
Advertisement
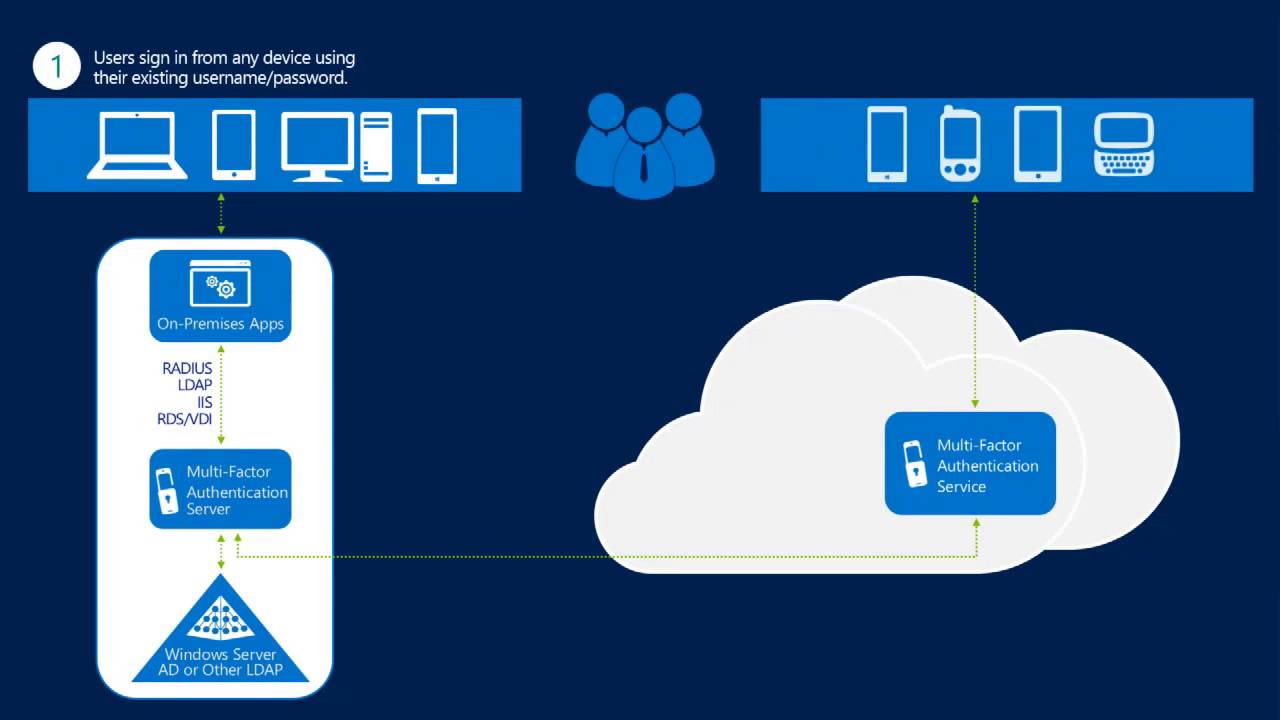
Azure Multi-Factor Authentication is a professional security and privacy program that gives you an extra layer of protection against identity theft. The program appears to be highly functional because, after logging in with your password, you must either enter a code sent to your phone or scan your fingerprint. There will be an unsecured vector to attack if you just utilize a password for user authentication. With the entire identity criteria, the program adds to the security, and your security…
Google Authenticator enhances security by generating two-step verification codes for your Google Account. Launched by Google LLC, this app requires users to provide a second form of authentication when signing in. It works offline, generating codes even without an internet connection, making it convenient for use on the go.
Advertisement
5Authy
Authy provides a two-factor authentication (2FA) service that sends text messages with verification codes for logging into protected accounts. The app allows synchronization across multiple devices, ensuring that you can access your codes from both your phone and computer. You'll receive notifications whenever someone attempts to access your account. When you log in to an account protected by Authy, you will receive a text message, which is one of the finest ways to implement two-factor security. It features a capability…
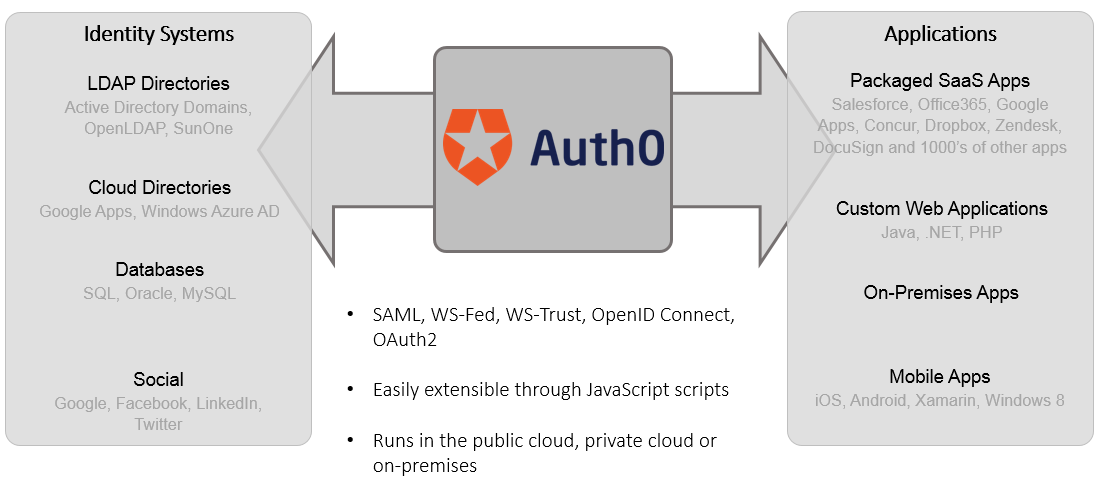
6Auth0
Auth0 is an all-in-one software solution that provides an authentication and authorization management platform that works with almost any digital device on the market. It's also compatible with mobile devices, IoT devices, computers, and applications. It has a lot of cool modules, and it's usually used by companies that support B2B, B2C, and B2E for universal identity. Many fascinating modules make up the platform's primary features. Universal login flow, customer domain, audit logs, universal login, SMS port, white-label manufacturer, brute…
Advertisement
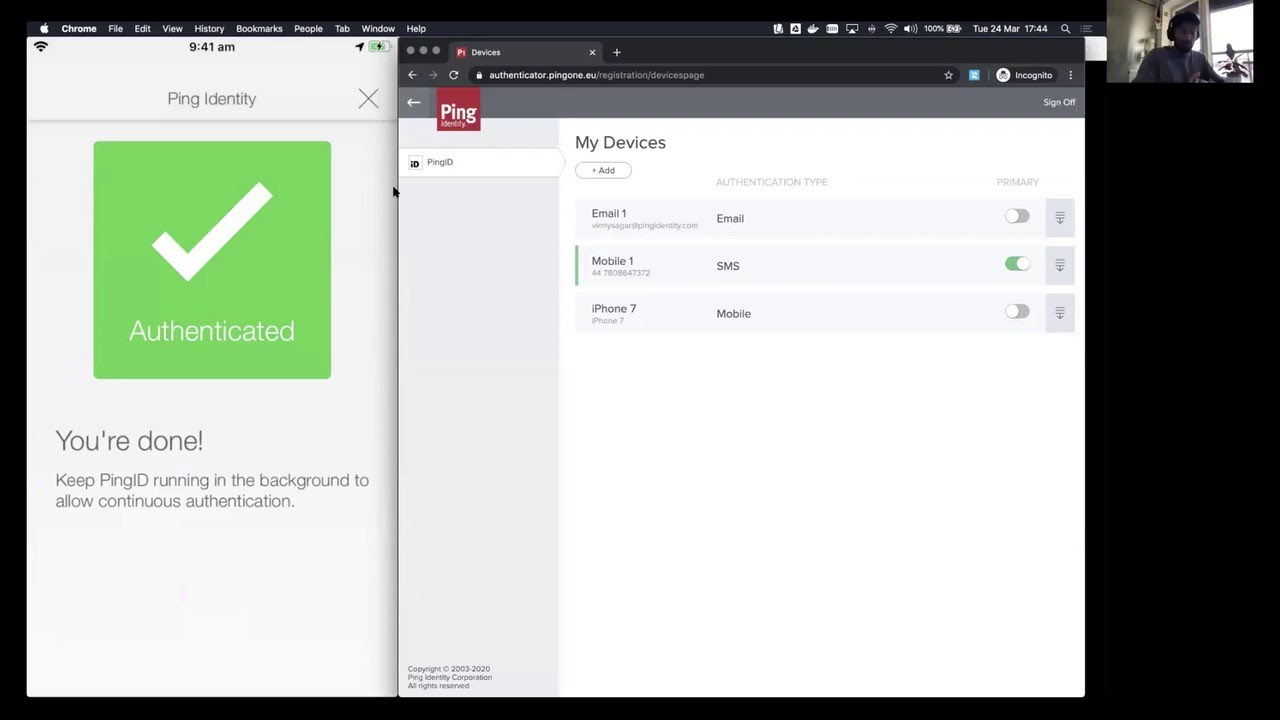
7PingID
PingID is a cloud-based strong authentication system that lets users log in to apps using their phones. PingID provides an easy-to-use solution for end-users while still providing the protection that administrators want. When strong authentication is required, end-users receive a message on their device, which also includes offline support if the device is not connected to the internet. Its robust network security safeguards networks, individual PCs, services, and businesses. With multi-cloud compatibility, it comes with the necessary digital transformation, allowing…